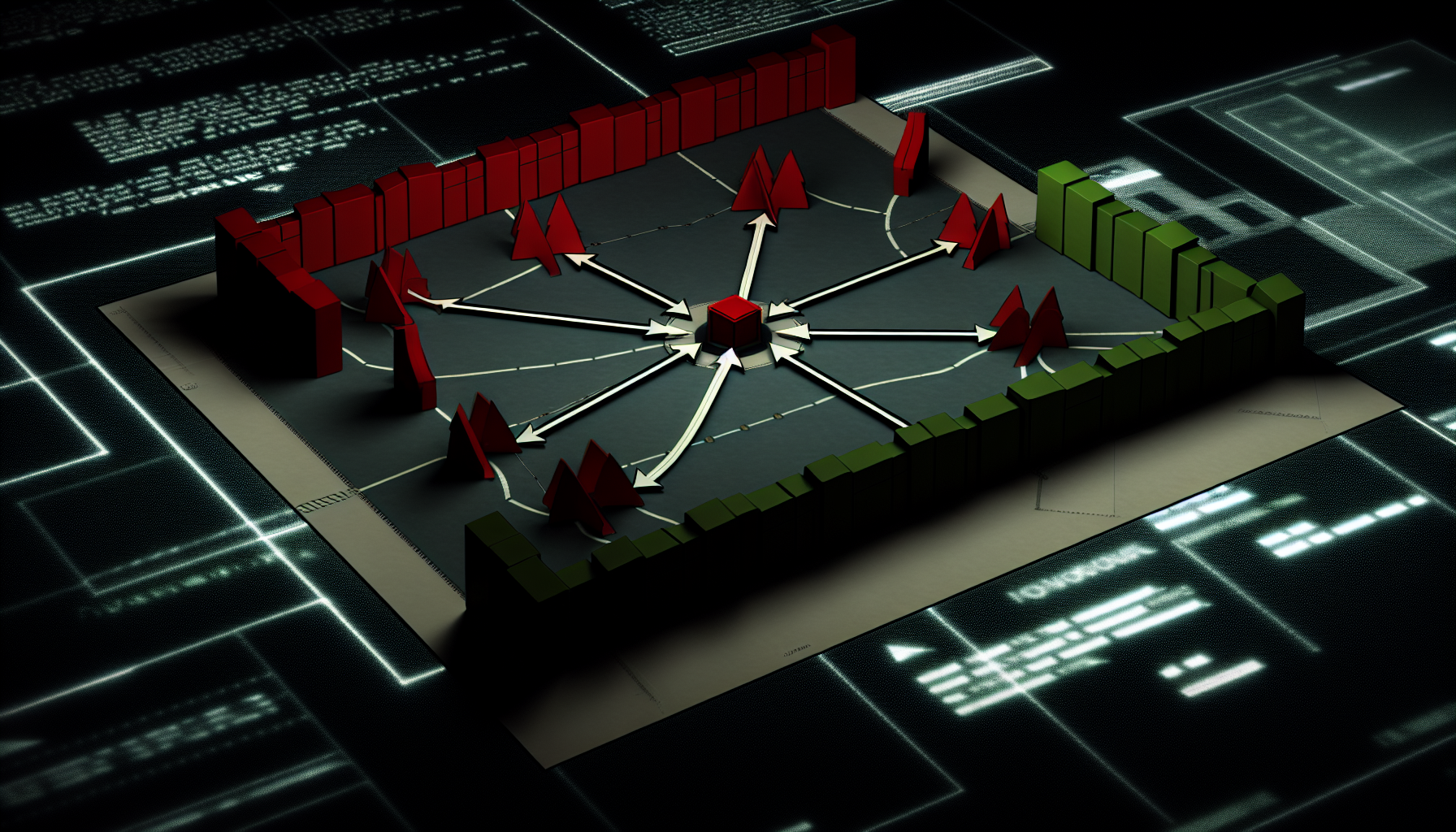
The threat model has shifted. A decade ago, detecting intrusion meant looking for network anomalies or unusual authentication patterns. Today, the challenge is simpler and harder: stop a single infected host from becoming a bridgehead into your entire infrastructure.
The reason is straightforward. Modern attackers don't need to compromise your entire network in one move. They need one foothold—a developer's laptop, a support technician's workstation, a contractor's VPN session. From there, lateral movement becomes the play. Network reconnaissance, credential harvesting, privilege escalation, and lateral spread across systems happen in hours, not weeks.
Why Single-Host Compromise Is Now a Containment Problem
In the shared hosting and managed infrastructure space, the risk multiplies. If your hypervisor is compromised, the blast radius is every virtual machine on that physical server. If a cPanel administrator's credentials are harvested, the attacker has keys to hundreds of customer accounts. If a mail server is turned into a spam relay or phishing platform, your entire IP reputation degrades.
The classic assumption—that a firewall and intrusion detection system will catch bad behaviour—breaks down when the attacker is already inside. They don't probe from the edge; they move laterally, often using legitimate administrative tools and credentials. They exfiltrate quietly, live off the land, and touch as few unique files or processes as possible.
For infrastructure operators, this means the detection and isolation problem has become primary. You can't assume your perimeter is perfect. You have to assume compromise and design for rapid containment.
Segmentation as Your Primary Defence
True network segmentation—not just VLANs, but enforced compartments with explicit allow rules—is no longer optional for serious infrastructure. A compromised web server should not have network access to your database cluster. A developer workstation should not route directly to your backup storage. A customer's VPS should not be able to reach your hypervisor's management interface.
This sounds basic, but implementation requires discipline. Every firewall rule, every routing policy, every trust relationship becomes a potential lateral movement path. In complex networks with hundreds of services, this audit is substantial work. But it's the difference between losing one customer's data and losing everyone's.
Zero-trust principles apply here. Assume every network segment is untrusted. Verify identity and authorisation for every connection, regardless of source. Use application-level authentication rather than relying on network topology alone. Microsegmentation—isolating individual services or even individual instances—is more work but drastically reduces blast radius.
Detection Without Noise
Segmentation buys you time and containment. Detection determines whether you catch the breach before it causes damage.
The challenge is separating legitimate behaviour from compromise. A host that suddenly contacts 50 internal IPs on ports it's never spoken to before is clearly suspicious. A host that exfiltrates 20 GB via HTTPS to an external IP might look like a large backup, especially if the SSL certificate is valid and the traffic pattern matches business hours.
Endpoint Detection and Response (EDR) agents provide visibility into process execution and file activity that network logs alone cannot see. They can alert on suspicious child processes, unsigned binaries spawning from legitimate applications, or unusual registry/configuration changes. However, if your EDR is not actively monitored—or worse, if alerts are treated as noise—it becomes security theatre.
For hosting operators, the additional consideration is customer transparency. If you're monitoring customer VPS instances for signs of compromise, you need clear policy and consent. Many customers expect privacy within their rented infrastructure. Detection and response mechanisms must balance security operations against customer expectations and legal obligations.
Incident Response and Rapid Isolation
Detection is useless without action. The response procedure must be clear, tested, and executable in minutes, not hours.
Automated isolation is critical. The moment a host is flagged as compromised—whether by human analyst or automated rule—it should be automatically disconnected from trusted network segments. This might mean disabling its network interface, blocking its MAC address at the switch level, or revoking its VPN credentials immediately. The key is speed and decisiveness.
For hosted infrastructure, this creates operational challenges. Disconnecting a customer's VPS without warning disrupts their service. You need a rapid customer notification protocol and clear contractual terms allowing emergency network isolation. Some operators implement a brief quarantine—network isolation with logging enabled—to preserve forensic evidence while containing spread.
Forensic capture should happen in parallel. Before wiping and rebuilding the compromised host, preserve memory dumps, filesystem images, and all logs. This serves both incident investigation and legal/regulatory requirements. However, forensics must not delay isolation; isolate first, investigate second.
The Practical Reality
Building infrastructure resilient to single-host compromise requires investment in architecture, tooling, and operational discipline. It also requires accepting that perfect prevention is impossible. Attackers will find footholds. Your goal is to ensure that one foothold does not become total system compromise.
For organisations running hosting platforms, this translates into network architecture reviews, EDR or Host IDS deployment, incident response runbooks, and regular tabletop exercises. For customers renting infrastructure, it means understanding your provider's segmentation and isolation capabilities and asking direct questions about breach containment procedures.
The organisations that will survive the next wave of breaches are those that treat lateral movement containment not as a feature, but as a foundational requirement.